Fraud Prevention Tips And Trends For 2017
2017 Cyber Security Predictions
2017 is now upon us and cyber criminals are increasingly making huge sums of money by stealing sensitive and private information via attacks on consumers, the largest of corporations, and governments. While nearly impossible to guarantee immunity from these attacks, being informed and prepared for them can limit your exposure to these cyberthieves.
1.) One of These Areas of Interest Now and into the Future is the Need for Improved Security on "IoT" Devices
With the ever-growing popularity of wirelessly connected devices such as smart watches, exercise and activity trackers, medical devices, and even utility smart meters, the pressure for improved security will increase dramatically in the years to come.
By 2020, the Internet of Things (IoT), or network of physical objects-devices, vehicles, buildings and other items which are embedded with electronics, software, sensors, and network connectivity, which enables these objects to collect and exchange data, will be close to *30 billion* strong and will affect every aspect of our lives.
Perhaps the scariest industry involved is with medical devices such as pacemakers or insulin pumps, which have been hacked before in "proof-of-concept" security research. With the further development of mHealth (mobile health), more of these medical devices will be transmitting via public networks, running through our own cell phones, computers, and tablets, and be loaded with perhaps the most sensitive data of them all.
2.) Apple's Popularity and Its Devices Will See Increased Attacks
Do to its surge in popularity, Apple devices are increasingly being targeted in malicious attacks such as malware and ransomware. While still relatively low frequency compared to PCs and Android devices, the growth of these attacks has been steady and even spiked during the last 18 months. Cybersecurity brokers have gone so far as to offer bounties for uncovering Apple vulnerabilities, with a cool $1,000,000 paid recently for a jailbreak of iOS 9.1!
Apple users need to be just as diligent with their cybersecurity as PC and Android users, because the faulty notion that Apple products cannot be hacked is a fairy tale. As any accomplished hacker will tell you, if it's connected to the internet, it can be hacked.
3.) Ransomware Gangs and Syndicates Will Grow Stronger
Ransomware, or a program that installs itself uninvited with the intention of rendering your device unusable until a fee is paid to remove it, has evolved and been growing from its roots in Russian speaking countries into Western Europe, North, Central and South America, Australia, and Asia.
Because of the profitability of these malicious programs, more established criminal gangs are getting in on the action, and we'll see the frequency of this type of attack increase.
4.) Cyber Insurance Will Become Commonplace Due to Increased Attacks and Breaches
The reason for cyber insurance's inception is due to two main factors: new state and federal regulations and the increase in cyber crimes such as payment fraud and identity theft.
Cyber attacks and data breaches can harm a company and/or brand, cause business interruptions, and are very expensive. With IT defenses often inadequate, cyber insurance has become another layer of protection.
Evolving as fast as the technology surrounding it, the core coverage of cyber insurance today was not available as little as three years ago. These greater coverage options will continue to grow and change, and many enhancements will be added in the coming years.
5.) Critical Infrastructure Will be Targeted by More Serious Attacks
With critical infrastructure being exposed by greater connectivity, utilities like water treatment plants, electrical grids, and nuclear power plants will become the targets of the future. Costing significantly less than a conventional war, cyberwars committed by criminals and governments are becoming the invasion of choice. Industrial IoT is becoming more connected than ever in order to meet the demands and requirements for reporting and improved functionality, and it will not be long before we see such a catastrophe happen.
6.) Encryption Becomes Even More Paramount to Security
With the amount of communications and data being transferred these days, encryption has naturally become even more important. With so many of the transfers going across unsecured and vulnerable networks, hackers have an easy time stealing the information or data they need.
Far too many of the new devices and applications' developers have neglected these important vulnerabilities, and it makes them high value targets for cybercriminals. This is where beefed up encryption can help.
But not all entities are welcoming this new age of stronger encryption. Both governments and law enforcement have decried it, saying it could be a hamper on their spying efforts.
7.) Governments and Corporations Will Utilize Security Gamification to Promote Security Awareness
As much as technology is king these days, the human element of internet security is every bit as important, if not more so, in keeping data secure. Social engineering is often used in targeted attacks, and simple knowledge of fraud tactics can save a consumer from becoming a victim as well.
In the same way the "like" button conditions users of Facebook to interact more, security gamification can teach end users and consumers alike to practice lasting changes to their risky internet behaviors. For example, security gamification could be used to train end users to to be mindful of phishing scams, or to create and use stronger passwords.
In conclusion, as technology sees exponential growth and advancement, we need to become more aware of its security risks as much as its benefits. The Internet of Things will eventually encompass everything we see, touch, and hear; and if we're not careful, all the data we deem important will be at great risk and possibly used against us.
The Romance Scam
You become emotionally involved with someone you've been communicating with on an Internet dating site. Your love interest tells you he/she is moving out of the country for work or wants to fly to your city to meet you, and asks you to wire money to help. If you fall for it, you'll receive more excuses and requests for more money, until you realize you've been scammed.
He told her he was a Connecticut contractor. She was a 67-year-old widow. After they met last year through ChristianMingle.com, an online dating site, he sent her a photo and wooed her with romantic words.
Three months into the relationship, she began wiring money to help him. He had gone to Nigeria to oversee a project, he explained, but ran into one emergency after another. She sent $15,000, she says, before realizing the suitor was a scammer.
"I had lost my husband of 40 years; I was just looking to find love like everybody else," says Pat, a Missouri businesswoman. "You're lonely, so you fall for it."
Online scams are as old as the Internet, but those that use romance as bait are on the rise as dating sites proliferate, authorities say. In 2012, the Federal Trade Commission created a separate category for them among the web crimes it tracks: "romance scam." Last year, the agency says, it received complaints of losses totaling $105 million, roughly even with the year before.
"The complaints reported are only a tip of the iceberg," says FTC director Steve Baker.
The U.S. Army Criminal Investigation Command calls the problem "epidemic." It says it receives hundreds of reports each month from victims bilked by individuals on dating sites who impersonate soldiers, including servicemen who have been killed in combat.
"Perpetrators are asking for money to purchase 'leave papers' from the Army, pay medical expenses from combat wounds or fly home from the war zone—all [items] taken care of by the military," says spokesman Chris Grey, who has spoken with victims from the U.S., Australia, Japan and Britain.
Ahead of Valentine's Day, Western Union has joined the Better Business Bureau in a campaign to warn consumers against sending money to anyone they haven't met in person, warm feelings notwithstanding.
The wire-transfer company ranks romance scams among the most prevalent types of global fraud it sees, alongside certain kinds of Internet purchases and fictitious lotteries. Canada's fraud unit reported $16 million lost to romance scams in 2012, up from about $600,000 in 2008. Authorities in the United Kingdom and Australia have also reported widespread problems.
Phil Hopkins, Western Union's security chief, has traveled to Africa, where much of the fraud originates, to discuss the problem with law enforcement there. He says loosely structured fraud rings and lone schemers elude detectives. And perpetrators based outside the U.S. are tougher to prosecute.
In a statement, ChristianMingle.com says it has "extensive safeguards…to protect its members, identify questionable profiles and eliminate attempted fraudulent activity." Spark Networks Inc., which also owns the Jewish relationship site JDate, says every new member must pledge not to send money to anyone they meet online and to report anyone who requests financial information on joining the site.
Criminals typically court victims over several months with poetry, flowers and other forms of flattery. They then lure victims off the dating site to communicate by email or instant message. Trust won, the perpetrators then present a crisis that requires money to resolve.
In San Jose, Calif., a 66-year-old woman dipped into her retirement savings and refinanced her house to invest $500,000 in an online suitor's fictitious oil rig, according to the Santa Clara County District Attorney's Office. The woman, who wasn't named, sent the money in allotments, ending with $200,000 transferred to a Turkish bank.
When she contacted the district attorney's office, it requested that the bank freeze the funds. An accomplice of the perpetrator, who is still at large, was arrested when he tried to withdraw the funds, and remains in jail in Turkey pending his case there. The bank returned the woman's money.
Santa Clara County prosecutor Cherie Bourlard says it was a miracle anyone was caught. The victim is likely to lose her house because she won't be able afford to pay the mortgage after the refinance, she says.
After this case was publicized, Ms. Bourlard says, she got calls from victims in South Carolina, Connecticut, New York, Washington and Brazil.
Shelley Bernhardt, Western Union's consumer-protection director, has been giving presentations at events hosted by organizations such as AARP to raise awareness among senior citizens, whom she calls especially vulnerable to romance scams.
Pat, the widow who was scammed, said her suitor's plot was so elaborate that even the "nanny" of his children called to vouch for his character, speaking in American-accented English. When she realized she had been duped, Pat says, "You don't want to talk to anybody about it, because you feel so stupid."
Still, she didn't give up on looking for love. She used the dating site until her subscription expired.
But four out of six suitors she connected with were scammers, she realized. Each time one asked for money, she replied: "I have been down this road before; you find another sucker."
The Disaster Scam: After a natural disaster like a flood or an earthquake, you receive a letter asking you to help the victims by sending money through a wire transfer. Never transfer money to people or organizations you don't know. If you want to make a donation, give it through a trusted organization where you understand how the funds are being collected and used.
The Relative In Need Scam: You get a call from someone pretending to be a family member or relative, like a grandchild, who's in trouble. Or, the caller pretends to be a lawyer or police officer who is with your family member. They may say the family member needs money to be bailed out of jail, or to pay a fine or for emergency car repair or medical care. If you're not sure that this call is really from a family member, don't fall for this fraud.
The Check or Money Order Scam: Someone sends you a check or money order, maybe for something you're selling through a classified ad or online, maybe as advance payment for a job you think you're getting. The amount is more than it should be. The scammer tells you to cash or deposit the check or money order at a bank, then wire the amount they've “overpaid” back to them. The check/money order turns out to be counterfeit, and you can't get back the “extra” money you sent by wire transfer.
The Internet Purchases Scam:
You're shopping online and find something you want at a price that seems too good to be true. It may be anything - a puppy, a car – or even an apartment to rent. It could be a place to stay on your vacation. And the deal is too good to be true. The scammer will tell you to pay with a money transfer. You may even get a letter or email with a receipt. Do not wire money for Internet purchases. You won't get the merchandise or rental, and you'll lose your money.
The Lottery Or Sweepstakes Scam: You receive an official-looking notice by mail or email saying you've won a large sum of money, possibly even including a check. To claim your valuable prize, you are asked to deposit the check and send a money transfer to cover taxes and processing fees. Be aware: if you don't remember entering a lottery, you didn't win. And never send money to receive money. No legitimate lottery or sweepstakes asks for money up front.
The Mystery Shopper Scam: You get hired to be a mystery shopper. Your first task: evaluate the customer service of a retail store. You're given a check to cash and use for purchases in the store, yet the amount of the check is more than it should be. The scammer tells you to wire back the amount they've overpaid. The original check was counterfeit, and you can't get back the money you sent by wire transfer, so you lose both amounts.
The Vehicle Purchase Scam: You find a great deal for a car online or in an advertisement. You contact the seller, who tells you to send the down payment through a money transfer, so you can avoid sales tax. He or she may even send you a “receipt” saying you've bought the vehicle. Do not send a down payment through wire transfer. You won't get the vehicle and you won't get back the money you wire.
The Fake Loan Scam: You receive an email or a letter from a fake loan company, offering to loan you money. All you need to do is send them money through a wire transfer to pay for loan fees, taxes, service fees, or advance payments. Never send money to a loan company to get a loan. It doesn't work this way. You will not get the loan, and you will lose the money you wire.
The Newspaper Ads Scam: You see something you'd like to buy in a classified or other ad in a newspaper. You're asked to pay for it through a money transfer. The price seems too good to be true. It is. Never use a money transfer to purchase an item from a stranger. You may never get the item, and you'll lose all the money you send.
Nigerian Scams (also called Nigerian 419 scams), are a type of advance fee fraud and one of the most common types of confidence frauds in which the victim is defrauded for monetary gain.
If We Are To Stay Ahead Of The Fraudster, we have to be able to read these trends and manage both our strategies and risks accordingly. In highlighting what we see as the trends, we aim to contribute to the debate and raise awareness of the risks. By keeping this debate alive we hope that fraud prevention will shortly gain an even greater emphasis in key seats of power – be that in the boardroom or within key government departments.
FRAUD TRENDS For 2017
1. With more high quality data becoming available to fraudsters than ever before, an world economies forecast to contract and the UK's and U.S.A.'s benefits spending being reduced, overall fraud levels will continue to increase dramatically across the US, UK and the rest of Europe. Fraud hotspots most likely to be affected in 2013 include: banks and card companies, insurers, online merchants, retailers and government agencies.
2 . The types of fraud likely to see the biggest growth will be CNP (Card Not Present) card fraud, other forms of cybercrime, internal fraud, and supply chain fraud. Procurement fraud is also set to rise significantly. In contracting (shrinking) economies, evidence suggests that people inside this function can be put under pressure to defraud.
3. Mortgage fraud is also set to surge in 2013, with credit rating experts pointing the finger at further rises in first-party fraud – i.e. where people misrepresent their finances whilst applying for mortgages. Once again the economic climate is a significant contributor to this.
4. Recent spectacular mass data breaches and suspicion of cloud security in some areas will continue. An increasingly greater emphasis will be placed upon PCI DSS and other data security and integrity issues. Already, the daily number of automated attacks on bank and retailer systems runs into the millions, which means that we will continue to see major high-profile data breaches both reported and otherwise .
5. Solutions will be based around systems for acquirers, online merchants and PSPs, who are regularly the victims of CNP (Card Not Present) fraud – where fraud is growing fast in line with the growth in internet based payments. Increasingly, solutions will move to better and newer generations of screening, scoring and risk based monitoring, such as those based upon Bayesian based fraud detection systems. These will start to pose a real challenge to older systems based on ‘so called' Neural Networks.
6. Most people feel that there could be a lack of unified central direction and strategy from government. The lack of a pan-European strategy will also prevail. The UK government's response is divided between the NFA, the Cyber Crimes unit and the Cabinet Office's FED (Fraud Error and Debt Initiative). Some believe passionately that the lack of a unified central government strategy will drive up fraud significantly in 2013. On the positive side, at least some of the civil servants who have been involved in the NFA since the beginning are starting to gain real experience of the sector and an appreciation of the enormous challenges they face. The DWP is also tendering to get some real-world fraud strategy skills into their midst too, which should prove invaluable given the changes due with the Universal Credit.
7. The USA is increasingly ready for a policy U-turn on the adoption of signature as the CVM of choice. The US market will find it increasingly difficult to evolve in a global payment systems world without the protections offered either by PINs - or a 'next generation' solution . As the rest of the world is moving (or largely has moved) in this direction already, 2013 could see this U-turn as fraud increasingly migrates to the US.
8. Major insurers will continue to develop a strong and very credible fraud prevention solution based around the ‘ front end ' (underwriting stage of business) The emphasis on delivering a strong industry wide data-sharing drive will also continue to increase; although a whole re-think of the industry fraud register will be needed to address Data Protection Act requirements.
9. There will be a major shift in the presence, position and fraud service offerings of one or more of the major data-bureaus (such as credit reference agencies), as more solutions either move ‘in-house' or move to systems developed by a host of new players in various fraud sectors.
10. And there will be some surprises as there always are – whether they are policemen ‘on-the-take', another raft of politicians fiddling their expenses, or further high profile banks brought to their knees by (usually) rogue traders.
The IT channel is a high profile target for fraudsters because of the nature of products it is dealing with, whether this is via carousel fraud, company hijacking or bogus customer orders. By remaining extra cautious and realizing that when a deal seems too good to be true it normally is, with anti-fraud based awareness we can beat the fraudsters at their own game.
For Businesses/Merchants
The first scenario is based on incoming calls attempting to obtain personal information or credit card information. The caller will state there is an issue with the processing statement and in an attempt to correct the over-billing on the merchant account, the merchant must fill out new paperwork. A request is then made for a fax number or email address so the paperwork can be sent to the merchant. If the merchant were to fill out the paperwork and fax it back then the fraudster would obtain all of the personal identifying information. If an email address were provided to the fraudster, there is the opportunity for the email to contain a virus along with the receipt of the merchant's personal identifying information.
Another type of incoming call is where the fraudster identifies himself from Merchant Services. He then states that the last credit card transaction did not actually process so the merchant is required to give the caller that information. In both cases, the fraudster attempts to intimidate the merchant into providing the requested information by stating that the merchant's terminal would not work from that point until service personnel arrived on the following Monday.
Fight And Win Against Organized Retail Crime
An additional type of incoming call fraud is based on the caller stating that he is from a large company and wants to make multiple large purchases from the merchant. The caller will ask what the processing limit is for the merchant and request that the merchant call Customer Service for an increase so the proposed purchasing process will be expedited. Also the fraudster will request that the merchant provide a credit card number so that the merchant can be placed on the company's “first call” list.
The final scenario involved the fraudster stating that he is from a government agency or branch of the military. The fraudster will then attempt to make multiple purchases on multiple credit cards under the auspices of the government agencies procurement or purchasing guidelines.
Merchants Have to Find the Right Mix as Both Too Much and Too Little Fraud Prevention Can Drive Customers Away
A leading fraud prevention and risk management provider, recently commissioned a study of “connected” U.S. adults — or those with access to both a smartphone and a web-enabled computer — to learn more about how consumers perceive and are affected by online fraud. With consumers continuing to focus on the security of online transactions, the bottom line is that an ineffective fraud prevention program is not only bad business, it's bad for business.
The survey found that consumers will change their shopping behavior if they have a negative experience with a fraud protection system. In addition, the survey found that consumers feel more vulnerable to fraud online than when conducting transactions in-person. Eighty-eight percent of respondents regularly make a purchase or conduct a financial transaction online, and, nearly two in three (63%) consumers believe that more fraud occurs when conducting transactions online than in-person.
Getting The Mix Right is Difficult But Imperative To Keeping Customers
When merchants look for an effective fraud prevention solution, they quickly realize that one size does not fit all. The proper approach will effectively identify and protect against emerging fraud schemes while ensuring legitimate customers are not inconvenienced.
Through The Eyes of The Consumer
As more commerce continues to move online, understanding consumers' security concerns and preferences relating to transacting online will be crucial in maintaining a competitive edge. According to the survey, consumers today are conducting the most online transactions in the retail industry (57%), followed by banking and finance (51%), travel (27%), music and movie downloads (24%), and entertainment industries (18%).
Consumers are increasingly thinking about security in choosing where to take their business. Effective fraud prevention programs are quickly becoming an integral part of online merchants' business models to appeal to the tech savvy, smart phone using, tablet-toting consumer.
The survey also found that consumers are starting to do more transacting online using newer popular devices, such as tablets and smartphones. Presently, online shoppers find computers more trustworthy than tablets or smartphones when making online purchases: 81% of respondents perceive their computer to be the most secure device for online shopping whereas only 7% trust their smartphone and 3% trust their tablets.
Consumers are more likely to patronize retailers who properly execute their transactions. So getting the mix right, not too much and not too little fraud prevention is imperative to keeping and getting (new) customers.
Current areas where mail order, telephone order, and Internet fraud are most prevalent include:
* West Africa (Nigeria, Ghana, Gambia), Asia (Indonesia, Singapore)
* Eastern Europe (Bulgaria, Romania, and Russia)
Suspicious Behavior and Unusual Requests
Relay Calls: A relay call is an operator-assisted telephone call, usually used by someone who is hearing impaired. While this is a valid service, criminals are also using the service to place fraudulent orders.
Customers Ordering Large Quantities of the Same or Similar Item:
Customers who provide multiple card numbers for the same purchase, especially when the card numbers are only different by the last few numbers.
Requests for Overnight Delivery, Without Regard to Cost:
Customers who request immediate processing of the order and want the tracking number used for the shipment ASAP.
Customers who place phone orders, requesting immediate processing of the order, and then advising they will have someone come to the store location to pick-up the product.
Requests for delivery to an alternate address, other than the billing address, or shipment to a freight forwarder. (Criminals will use United States based re-shippers to avoid detection of foreign shipments).
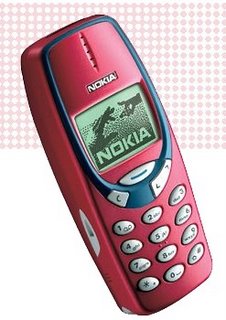
Requests for merchandise you do not sell. Most common requests are for cell phones and laptop computers.
Business Communication via a free email service (Yahoo, Hotmail, Gmail, etc).
NOTE: With today's technology it is possible to alter a photocopy of a credit card or personal identification such as a driver's license or passport. Sometimes a fraud order will include a faxed or e-mailed photocopy of the card to gain your trust. These photocopies do not guarantee that you are dealing with the correct cardholder. Always verify the order information with your Authorization center before proceeding with the order.
Four Quick Prevention Steps:
1. Before processing an order obtained via relay call, contact your Voice Authorization Center or place a direct call to the credit card issuer.
2. Verify the cardholder's address by using the Address Verification System (AVS). Your terminal can be set up for the AVS program, which allows you to include an AVS request with an authorization request. You will receive a result code indicating whether the address given matches the address the issuer has on file for that account.
3. Card Verification Value (CVV2) VISA and Card Validation Code (CVC2) MASTERCARD are verification requests that can be added to most terminals. This system will verify the three-digit code printed on the back of a credit card (or four-digit code printed on the front of an American Express credit card). You will receive either a "match" or "no match" response from the card-issuing bank if CVV2 is provided at the time of the authorization.
4. Authorizations: Get authorization for the full amount of the sale. Do not split a declined transaction into smaller increments to obtain an authorization. If an authorization request is declined, request another form of payment other than a credit card. (Be aware that there are counterfeit check schemes that involve overpayment with a counterfeit check and a request to wire the difference to the overseas customer. This causes a loss of both the merchandise ordered and the money that made up the difference.) An authorization code does not guarantee that a transaction will not be disputed later. An authorization code simply identifies that the amount of credit requested for this particular transaction is available on the card. An authorization code does not protect you in the event of a Chargeback regarding unauthorized transactions or disputes involving the quality or delivery of goods and services.
NOTE: Use of CVV2, CVC2, and AVS can lessen a non face-to-face transaction's risk of fraud by providing better information on which you can make a better business decision. However, CVV2, CVC2, and AVS do not eliminate Chargebacks, nor absolve the merchant of their liability for Chargebacks associated with processing credit card transactions. For more information about AVS and CVV2, CVC2, contact 1-800-725-1243. If you are an Internet merchant, contact your web provider for additional fraud settings that may be available to you through their service.
Useful Numbers and Websites:
VISA Merchant Verification Service-800-847-2750-AUTOMATED
Option 1, Address Verification: enter in the numeric portion of the street address, zip code, and VISA card number, and it will advise you if there is a match
Option 2, Issuing Bank Phone numbers: enter the VISA card number and it will provide you with the 800# for Issuing banks if available.
MasterCard Assist-800-622-7747
Select your language preference, then Option 2. Enter the MasterCard card number and it will provide you with the 800# for Issuing banks if available.
Discover Address Verification-800-347-7988-AUTOMATED
You will need your Discover Merchant number. Enter the Discover card number and address information, and it will advise you if there is a match.
American Express Address Verifications-800-528-2121
Option 3 allows you to verify the name and address of a particular AMEX card number.
Visa.com:VISA brand information. Includes tips, regulations, news, and fraud features. (Choose option for Merchants/Businesses)
Next-Generation Bug / Microwave / ELF / Spy Phone / GSM And Camera Detectors (Buy, Rent, Layaway) tinyurl.com/2eo8mlz Open...
— Spy Store Rentals (@MontyHenry1)
Nanny IP (Internet) Cameras, GPS Trackers, Bug Detectors and Listening Devices, etc, (Buy / Rent / Layaway): tinyurl.com/396jlw6...
— Spy Store Rentals (@MontyHenry1)
• Video is Recorded Locally To An Installed SD Card (2GB SD Card included)
• Email Notifications (Motion Alerts, Camera Failure, IP Address Change, SD Card Full)
• Live Monitoring, Recording And Event Playback Via Internet
• Back-up SD Storage Up To 32GB (SD Not Included)
• Digital Wireless Transmission (No Camera Interference)
• View LIVE On Your SmartPhone!
Includes:
* Nanny Cameras w/ Remote View
* Wireless IP Receiver
* Remote Control
* A/C Adaptor
* 2GB SD Card
* USB Receiver
FACT SHEET: HIDDEN NANNY-SPY (VIEW VIA THE INTERNET) CAMERAS
Specifications:
Receiver Specs:
* Transmission Range of 500 ft Line Of Sight
* Uses 53 Channels Resulting In No Interference
* 12V Power Consumption
* RCA Output
* Supports up to 32gig SD
Camera Specs:
* 640x480 / 320x240 up to 30fps
* Image Sensor: 1/4" Micron Sensor
* Resolution: 720x480 Pixels
* S/N Ratio: 45 db
* Sensitivity: 11.5V/lux-s @ 550nm
* Video System: NTSC
* White Balance: Auto Tracking
* You Buy Our DVR Boards And We'll Build Your Products! (Optional)
Our New Layaway Plan Adds Convenience For Online Shoppers
Phone: (1888) 344-3742 Toll Free USA
Local: (818) 344-3742
Fax (775) 249-9320
Monty@DPL-Surveillance-Equipment.com
Google+ and Gmail
DPLSURVE
DPLSURVE
MSN
Monty@DPL-Surveillance-Equipment.com
AOL Instant Messenger
DPLSURVE32
Skype
Montyl32
Yahoo Instant Messenger
Montyi32
Alternate Email Address
montyi32@yahoo.com
Join my Yahoo Group!
My RSS Feed